cyber-security
Cybersecurity Market Update
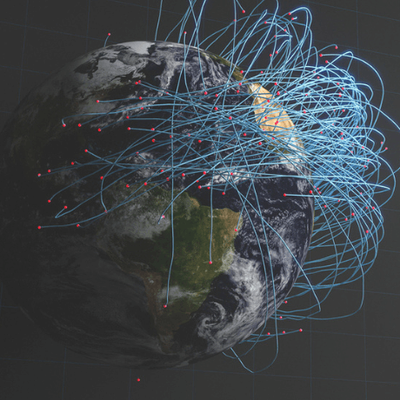
Glocomms' insight on the 2018 Cybersecurity Landscape Across the End-User and Vendor ArenasIntroductionGlocomms was founded on the premise of Cybersecurity becoming the most in-demand and integral part of technology across all industries. In 2017, we saw a multitude of high-profile cyberattacks targeting various companies including Uber, Deloitte and Equifax with the most prominent attacks being WannaCry and Petya. Given the visibility on the cybersecurity market, Glocomms expects to see a large focus on hiring resources and talent to develop and elaborate the hardening of security practices. Such developments include in-house security operation centers (SOC), increased spending on the most innovative threat intelligence products and AI talent and the adoption of automation and cloud security practices in order to properly protect customer and employee data.The consequences of insufficient security and data protection were recently highlighted by Facebook stocks sliding nearly 15% in a 36-hour window, off the back of an exposed global data breach. Such high profile examples prove that Cybersecurity has the attention of the global media platform and consequently, the market is tightening as the need for remediation in real-time is becoming absolutely imperative.In order to provide this level of service on a 24x7x365, vendors and end users are adopting advanced solutions. The two main trends we have seen in the first quarter of 2018 have been the integration of Artificial Intelligence & Data Science coupled with the need for Automation & Cloud Security. AI/Data Science & Cloud AutomationOur recruitment business gives us a unique look into these trends, as our business model is comprised of two main pillars of focus: Cybersecurity and AI/Data Science. We see the perspective of urgent needs for specific skillsets, as well as the perspective of building expertise through seeking new challenges and career options through working with stealth-mode to IPO vendors as well as the world’s largest global end-users.When considering the impact AI can have on Cyber, it is clear why artificial intelligence, machine learning and data science will have a huge impact on the ability for software to be able to detect and remediate intrusions and vulnerabilities. Nonetheless, it is who brings the expertise that affects how analytics will impact the industry given these will be the individuals building models to analyze and make sense of the data.In order to understand the talent pool, we need to understand what motivates individuals to bring their experience to the cybersecurity industry. Most frequently, we see these professionals are motivated by the exposure to working with novel, proprietary, and in this case, unknown data. Additionally, not only the access and exposure to the data is compelling, but also the advanced decision making predictable by the data that draws this talent into the industry.We have also seen increased attention on the automation and acceptance of risk adverse cloud usage cases, the adoption of MSSP’s that offer integrated threat analytics/ threat management solutions, and new industry trends that dive deeper into the impact AI can have on this ever-changing landscape across the vendor and end-user arenas.Artificial intelligence, machine learning and data science are being leveraged in a variety of ways and can be exhibited by the huge influx of neural network and deep learning talent transition into the threat analytics arena. Given the sheer magnitude and significance of personal information embedded within the data across industries such as healthcare, financial services and commerce, it is no surprise that data scientists are excited about an opportunity to advance security solutions and play an impactful role on the business/product at large. We know from speaking to these professionals that it is the access and exposure to novel and unique data across the abovementioned industries that drive and motivate their career interests.Given that Data Science/AI & Cybersecurity are the two focal points of our Glocomms business, it is exciting to see the transfusion of these emerging technology industries shaping the future of the entire technology landscape across all industries.Investment BanksCloud security is currently the hottest trend from an end-user perspective. This trend is clear, given the activity we have seen across the finance industry as they move towards the adoption of specific usage cases for the various open source cloud platforms. This is exciting because these have historically been some of the most proprietarily kept platforms in the world – some banks even used proprietary coding languages to build their platform! In order to be comfortable with these offerings, the institutions now need to put together documentation on the risk assessments attributed to such solutions. Once these frameworks and usage-cases are clearly determined and outlined, offerings will begin to spread across more and more business units. Currently, large asset managers and global investment banks offer their clients a commercialized version of their front-office risk systems but this is only one portion of what the cross-business platform has to offer.The next step will be providing an integrated and secure cloud-based solution across all layers of the risk management platforms that each of the various firms offer. Some banks are in the midst of developing a similar type of cross-business platform and although they may be scrutinized for their late-arrival to the party, it might work to their advantage given the new technology currently available because having an opportunity to build a platform from scratch using the latest and greatest products for hardening security layers and adopting cloud offerings allows for a more integrated and theoretically, hardened solution! It seems cloud security will be at the top of the list for most in-demand and least- attainable skill sets in 2018. This has already been evident given the vast hiring and increased compensation bands for cloud security professionals across the end-user arena. We believe the reason for this is these professional all need to not only bring the expert technical skills to the table, but also need to be able to communicate internally and externally with key stakeholders around usage cases for cloud offerings.Buy-Side PerspectiveFrom a Buy-Side perspective, we have seen large global hedge fund clients looking to hire Encryption Engineers to build proprietary security layers into their existing infrastructure (often cloud-based). This is an obvious step in the right direction, given in the past it seemed many funds were scared by the prospects of putting their ‘secret sauce’ out in the cloud. Additionally, we have seen vast hiring across the Security Incident Event Management (SIEM) arena, most of whom, seem to be moving to Splunk given the versatility of the product. This is also consistent with what we have seen in Investment Banks this year.From a recruitment standpoint, we see a huge amount of potential on the buy-side in 2018 and expect to see talents being directly targeted from the tech giants as these are the professionals with the most amount of exposure to novel data with the best skillsets for architectural remediation and hardening. Vendor PerspectiveAs the vendors continue to offer more and more comprehensive and integrated analytical solutions, the need to stay on top of the market and hire professionals that have experience with the most cutting-edge products becomes even more imperative. We have seen massive hiring across the vendor arena given the influx of investment and the urgent need for this analytical talent. The data being analyzed is ever-increasing and the adoption of AI is not quite keeping up with the workload for the SOC. Thus, we have still seen a steady stream of hiring within these types of positions including: threat hunters, incident responders and security engineers. Not only the vendors are hiring these professionals across the mid-senior level, but also the end-users are building their own in-house SOC’s to reinforce internal security measures creating more intelligent solutions on the network to detect vulnerabilities more quickly and readily. We have seen a large increase this year of around 20% higher than the industry standard this year in the compensation bands for someone with 3-5 years of experience with the abovementioned skills.Glocomms’ cybersecurity recruitment practice is broken down across the vendor and end-user arenas as we have a commercial practice that offers talent solutions for our vendors across the entire product development lifecycle.As mentioned above, the adoption of intelligent threat hunting, incident response and vulnerability management has been clearly exhibited in a hiring trend of AI talent into the vendor and MSSP arena. Candidate TrendsAn interesting trend to note has been the movement of security professionals from the defense industry transition and partner with the financial services employees, in an attempt to continue to broaden the level of expertise and attention on security related problems. This talent is coming out of New York, Boston, Washington DC Metro Area, Texas, and California and heading to new security hubs forming in the Atlanta, South Carolina, Minneapolis and Colorado.Additionally, we have seen a large interest on the Financial Services side to hire talent from the Tech Giants given their background and exposure to massive amounts of data, enterprise level architecture, and forwards thinking technical skillsets.Given the sheer magnitude of talent required, in the last 5 months, we have placed over 15 individuals for one Cybersecurity start-up that is still in stealth-mode on a retained basis! This project is ongoing and we expect to fill nearly 40+ roles this year with this one client given how perfectly our business models align, we have been able to deliverThus far in 2018 we have worked closely with a number of small to mid sized organizations (20-200 employees) on both Coasts undergoing large growth initiatives. Rapid growth is not uncommon for start-ups in this industry; these companies are primarily seeking analytical/AI talent, software engineers who are building their propriety platform and security professionals to advance the offerings. One interesting thing to note has been that security software engineers are receiving larger portions of equity given the impact their development of the platform will have on the multiplier attributed to the growth potential and in turn, value of the business.For this type of endeavor we recommend a Multi-Hire Campaign (MHC) as we are able to best align our services with a companies specific and often urgent needs directly impacting our clients’ growth through an all-encompassing recruitment solution.Many of our institutional clients are entirely revamping their security business units given the ever-changing nature of the available technology within the industry. As a result, we have staffed multiple senior, CISO/Strategic Leaders for our end-user clients whom will drive the growth initiatives going forward in 2018 and years to come. Mergers & AcquisitionsOur final cybersecurity market trend we wanted to highlight in this report corroborates the above with respect to focus and attention on new, cutting-edge, AI-driven threat management platforms. Security Vendors are being acquired by the big Tech Giants and large cyber players. The options are narrowing and the solutions are becoming far more comprehensive and integrated. Recent examples of this include: SQRRL were acquired by Amazon for $40 million; Phantom Cyber is being acquired by Splunk for $350 million; and CloudLock is bought by Cisco for $293 million. This showcases that the big-players are aware of the trends outlined above and are looking to eat up the market share and gain control of the growth and opportunity that is ravishing the emerging technologies marketplace. Diversity & InclusionDiversity and Inclusion awareness is at an all time high in the technology industry, with female representation and wage parity dominating the headlines. At Glocomms we find that identifying good practice, policies and initiatives to improve workforce diversity and inclusion are paramount for our clients. Throughout 2018, alongside our parent company, Phaidon International, we will be running a number of positive, action-orientated client events with relevant guest speakers and industry experts. The common themes of these initiatives will be to share pragmatic and proven successful practices that can tangibly improve diversity and inclusion within the workplace. By doing so our valued clients can enhance their access to wider talent pools for their meritocratic workplaces.In relation to Cybersecurity – this is one of the most homogenized verticals within the technology arena and female-talent is highly scrutinized for being absent. Males hold 3 out of 4 jobs in tech, but specifically within cybersecurity, the numbers reflect that only 14% of the U.S. workforce in cybersecurity is female. [1] However, out of all of the areas within technology, we believe that Cybersecurity is the field that truly needs a diverse talent pool.Working in Cybersecurity involves dealing with hugely complex issues and problems – teams need diversity so that problems are attacked with different viewpoints. At Glocomms we focus heavily on sourcing diverse talent within this field and working closely with our clients in creating a work environment to allow such talent to excel in their careers. In the past six months, 24% of the placements we have made in the Cybersecurity field are female. Whilst we still have a long way to go we are dedicated to doing our part to empower females to succeed in the industry.In addition to females, Glocomms is committed to contributing to and being the driving force of change across all marginalized groups with respect to Diversity and Inclusion. Most recently, on March 24th, Glocomms was a sponsor for the second annual Out in Tech Talks[2], an event that united 400+ leading and aspiring LGBTQ+ and allied voices to advance the dialogue around diversity in tech and address the power of tech to create social change. It was an incredible event, showcasing the progress achieved while illuminating the massive amount of work left to do in reshaping the industry. Impressive panels included the leaders in Diversity and Inclusion at Amazon, Linked in and Youtube, an MD/Business Leader for the Cybersecurity business at a Leading Global Investment Bank and our own Executive Director at Glocomms.Closing ThoughtsThis report was written and prepared by Giancarlo Hirsch, Vice President at Glocomms and accurate as of March 2018.Glocomms has offices in NY and SF and is looking to launch offices in Boston, Chicago, Dallas and Charlotte in the coming 18 months. For more information or to get in touch with the team at Glocomms, please do reach out to usa@glocomms.com!-------About UsGlocomms is a leading specialist recruitment agency for the technology sector. We were founded in 2013 to give clients and candidates peace of mind that the recruitment process is in expert hands. Our continual investment in best-in-class technologies and consultant training enables us to recruit with speed, precision and accuracy. Today, Glocomms provides contingency, retained search and project-based contract recruitment across our offices in San Francisco, New York, London and Berlin. Find out how Glocomms can help you.
Read More